
|
|
ICT-Hotlist Topic
Kaspersky labs has published an eBook with valuable tips about cybersecurity.
Published : 2016-03-31.
Last updated : 2017-05-02.
The eBook has the following chapters:
- Regularly talk to employees about cybersecurity.
- Remember that top management and it staff are employees, too! (This chapter might be a real eye-opener)
- Explain to the employees that, while you make the best effort to secure the company's infrastructure, a system is only as secure as the weakest link. (I'd rather not use the term weakest link with regards to end users. See also tip 7.)
- Have regular, focused sessions with employees to explore different types of cyber-attacks.
- Warn employees to pay special attention to social engineering activities.
- Train employees to recognize an attack.
- Never disapprove or make fun of an employee who raises a red flag. (A very important tip. Always thank the user for bringing a possible threat to your attention. For every 10 false warnings he/she might find a thread that bypassed your filters or even Antivirus solutions!)
- If an incident happens, give your employees a heads-up as soon as possible.
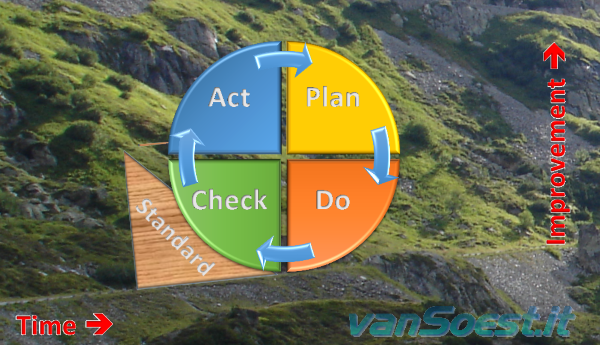
- Regularly test employee's cyber-security knowledge. (Another great example of a continuous improvement process (Deming)
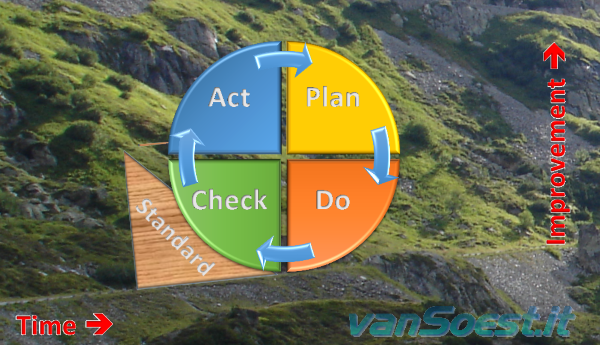
Deming Cycle of Continuous Improvement (Plan, Do, Check en Act).)
- Invite, listen and respond to feedback.
Read all the tips in detail here Top 10 Tips For Educating Employees About Cybersecurity
Scripts and programming examples disclaimer
Unless stated otherwise, the script sources and programming examples provided are copyrighted freeware.
You may modify them, as long as a reference to the original code and hyperlink to the source page is included in the modified code and documentation.
However, it is not allowed to publish (copies of) scripts and programming examples on your own site, blog, vlog, or distribute them on paper or any other medium, without prior written consent.
Many of the techniques used in these scripts, including but not limited to modifying the registry or system files and settings, impose a risk of rendering the Operating System inoperable and loss of data.
Make sure you have verified full backups and the associated restore software available before running any script or programming example.
Use these scripts and programming examples entirely at your own risk. All liability claims against the author in relation to material or non-material losses caused by the use, misuse or non-use of the information provided, or the use of incorrect or incomplete information, are excluded. All content is subject to change and provided without obligation.
|








 Back to the ICT-Hotlist...
Back to the ICT-Hotlist...