
|
|||
|
| Home |
| About |
| Hobbies |
| Software |
| Hardware |
| ICT Hotlist |
| Purpose |

ICT-Hotlist Topic

Business Continuity Management Example: selection process disaster / calamity preparation.
There is no ideal solution applicable for every company, but next selection process-diagram can help you prepare to combat a calamity.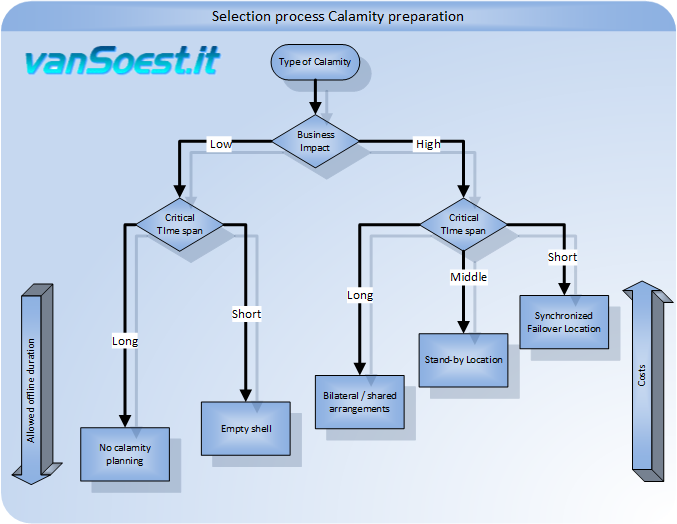
Picture 1. Example of a selection process disaster preparation
Business Impact.
The most important decision to make is whether the loss of all the ICT systems has a great impact on daily operations.For example: you will be fined when the VAT declaration is not done in time. You only have a single system for this task. When thorough analysis shows that the fine is less than the cost of the continuity solution; Why deploy a solution? There could be time enough to find a replacement server system and configure it.
Critical Timespan.
The next trade off for a solution may be the time frame in which the service should be operational again.For example: you have a call centre that requires a telephone exchange and a call-monitoring and invoicing system for handling the calls. The lack of these systems has a high business impact (no one can be called) and needs to be resolved as soon as possible as labour keeps costing money and billable calls stop immediately. In addition, there is a risk of data loss, so calls made before the calamity can no longer be invoiced.
Possible Solutions.
Why (not) choose a Cloud Business Continuity solution?
There are a number of considerations to be made about Cloud solutions for Business Continuity. One can choose an In-House, a mix of In-House and Cloud solutions or move every Business Continuity solution to the Cloud. With Cloud solutions one can easily purchase redundant capacity (Microsoft requires this for production environments). The management costs only rise as soon as the extra required capacity in the cloud solution is used during a calamity. Thus achieving an initial cost advantage compared to the solutions indicated in picture 1.There are some considerations against the placement of ICT-Systems and data in the Cloud:
- Localized storage of data: European legislation requires that certain information is stored within the borders of the European Community. Not all Cloud providers can guarantee this.
- Legal aspect: Who is the legal/rightful owner of the data? Are you as a customer owner of your data or is your supplier the owner once the data is uploaded?
- Patriot act/Freedom Act/Privacy shield: It would take too long to go in detail, however, to what extent do you trust your American partner, his American employees and their secret services handling your data?
- Back-up in the Cloud: Apart from the above considerations, there are excellent suppliers of backup solutions in the Cloud. Keep in mind, however, that the software on your systems is going to register what files have changed and only upload these (Delta technique). This gives you very little data traffic over your internet connection. Also restoring a single file or some files is simple on your existing internet connection. However, when you need to restore a file server, you will use your internet connection up to 100% for several hours and render it unusable.
- Migration and Vendor lock-in: Many Cloud/SAAS vendors provide import-functions to import your data and systems in their Cloud solution. Many vendors have no options to export your data (back) to your systems or to another Cloud supplier.
- Availability: Outages of cloud providers are getting more and more in the news because more companies rely for (all) their services on that cloud provider.
- Costs: Egress fees are often unexpected costs charged by cloud providers to move or transfer data from cloud storage (where it is uploaded and used by employees) to on-premise or cloud backup systems. These costs, also called bandwidth or data transfer costs, are separate from the costs organizations pay for monthly or annual cloud storage and processing licenses. Because moving files and data to the cloud provider is included in the licensing fee, outbound fees are often seen as a protective measure to prevent switching providers. Thanks to European legislation (Article 6.9 DMA) it is prohibited to charge costs for outgoing traffic as a protective measure to prevent switching to another provider when the service provider has been declared a Gatekeeper.
| Planning type | Description |
|---|---|
| No Calamity planning | Making no plans and prepare nothing can be an appropriate choice when thorough analysis shows that daily business operations minimally dependent on ICT solutions. Only at the moment of a calamity replacement parts or systems are purchased. The main advantage of this strategy is the low preparation cost. |
| Empty Shell | In the case of an Empty Shell an investment is done by preparing a computer room at a different location (fire separated, other network/power suppliers). This space is equipped with air conditioning, power and network connections, however the rapidly ageing server systems are not purchased and installed. This reduces the replacement cost. |
| Bilateral/Shared arrangements | In case there are good relations with a business in the vicinity of your business premises, you may be able to share part of your data-centre with the other company. At the same time, the partner shares part of its computer centre. Because of the downsizing of hardware and virtualization technologies, computer rooms build years ago have lots of spare space to place a rack servers of the other company. Business Continuity service providers share their computer centre with multiple customers to share their investment and make them quickly available in case of a calamity. |
| Stand-by location | An alternative computer room at some distance from the primary computer room, equipped with all systems and software, network connections, and cooling. The primary computer room and alternative space are geographically dispersed so both are not disabled during a fire/flood and/or power failure. |
| Synchronized fail-over location | This is of course the ultimum when planning against calamities. All information (emails, files, and databases) are automatically synchronized between the two locations by means of synchronous storage systems (SAN). Data at the primary location will only be accepted if they are also reliably stored in the alternate location. For performance reasons, the alternative location should not be located too far from the primary location. |
All these solutions are costly, the solution on the right in picture 1 is the most expensive but is able, when correctly implemented, to get the systems online in a very short time with minimal loss of data.
Also read:
- Business Continuity Management: an introduction.
- Business Continuity Management: Escalation procedure (ICT).
- Business Continuity Management Example: selection process failure preparation.
Glossary
- Asynchronous replication:
-
Technology where synchronization of data is performed between two or more systems by sending data from the source system to the destination systems without waiting for an acknowledgement of the destination systems. The source system guarantees that the data will be sent to the target systems.
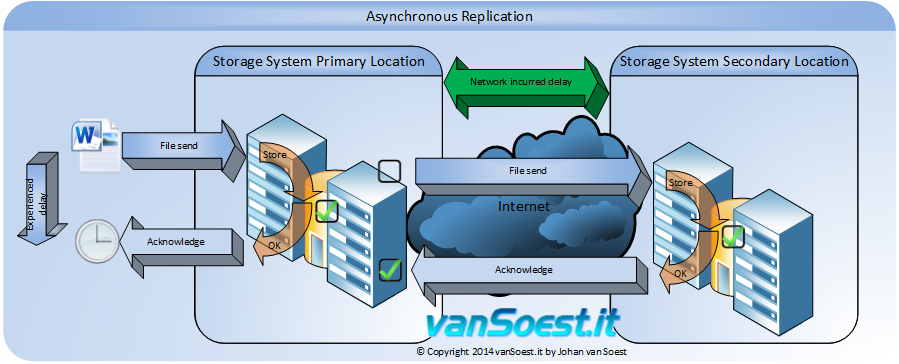
Picture 2. Asynchronous storage replication - Calamity:
- A calamity mostly arises from an incident of external origin that expands across multiple hardware systems, software
systems or even employees. These incidents include:
- Fire
- Economic boycotts
- Epidemics
- Hacking
- Floods
- Sabotage
- Software errors
- Storm damages
- Failing software updates
- Primary-location:
- Computer Centre or room housing the systems that daily process and store information.
- Production-location:
- Refer to primary location.
- Secundary-location:
- This term is interchangeable with the term "fail-over location". This is the location where the Business Continuity systems are prepared to take over the workload in case of a calamity.
- Server system:
- Complete but limited combination of software and hardware to support a task for a user. For example: a file storage service consisting of a server with many hard drives and an operating system for file storage and an application for version-control.
- Failure:
- In short: a failure is defined as a problem related to a program or a hardware component. Disturbances/failures can be solved with redundancy and high availability systems (HA)
- Synchronous replication:
-
Technology where synchronization of data is performed between two or more systems by sending data from the source system to the destination systems. The transaction in the source system is marked as correct and completed only when the update is send to the destination systems and marked as complete and correct.
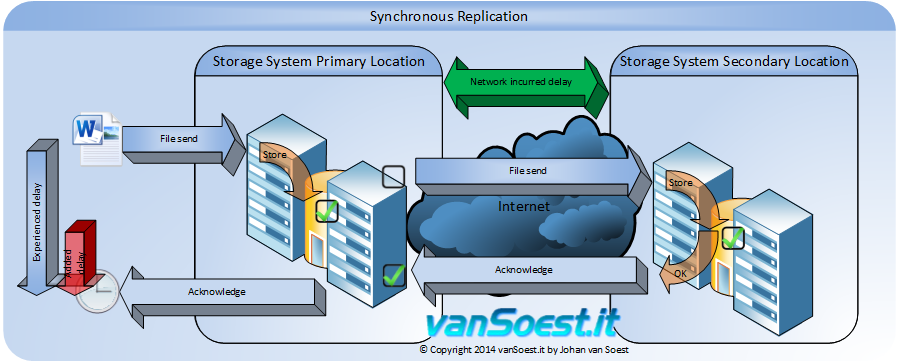
Picture 3. Synchronous storage replication. - Fail-over-location:
- Ref Secundary location.
You may vote your opinion about this article:





Scripts and programming examples disclaimer
Unless stated otherwise, the script sources and programming examples provided are copyrighted freeware. You may modify them, as long as a reference to the original code and hyperlink to the source page is included in the modified code and documentation. However, it is not allowed to publish (copies of) scripts and programming examples on your own site, blog, vlog, or distribute them on paper or any other medium, without prior written consent.Many of the techniques used in these scripts, including but not limited to modifying the registry or system files and settings, impose a risk of rendering the Operating System inoperable and loss of data. Make sure you have verified full backups and the associated restore software available before running any script or programming example. Use these scripts and programming examples entirely at your own risk. All liability claims against the author in relation to material or non-material losses caused by the use, misuse or non-use of the information provided, or the use of incorrect or incomplete information, are excluded. All content is subject to change and provided without obligation.

 Back to the ICT-Hotlist...
Back to the ICT-Hotlist...